Does The Cloud Provider Provide Vulnerability Scan
Does The Cloud Provider Provide Vulnerability Scan - This article delves into the complexities. Pci dss 4.0’s shift to authenticated internal vulnerability scanning marks a significant evolution in compliance and data protection. Qualys cloud platform has multiple modules that enable compliance, vulnerability scanning, malware detection, and cloud workload protection. Building a complete inventory of your it environment helps eliminate blind spots and ensures no critical assets are. Cloud security scanners are designed to identify vulnerabilities and other issues that could open up cloud environments to attack or create regulatory compliance or legal issues for a. Cloud vulnerability scanning is usually performed by specialized security tools that are designed to automatically identify common vulnerabilities, such as sql injection flaws. Vulnerability assessment— security center does not directly. Azure security center provides several capabilities that can help you scan cloud resources for security gaps: All of the main cloud providers need to be supported by your scanner. These automated tools scan the cloud infrastructure and.
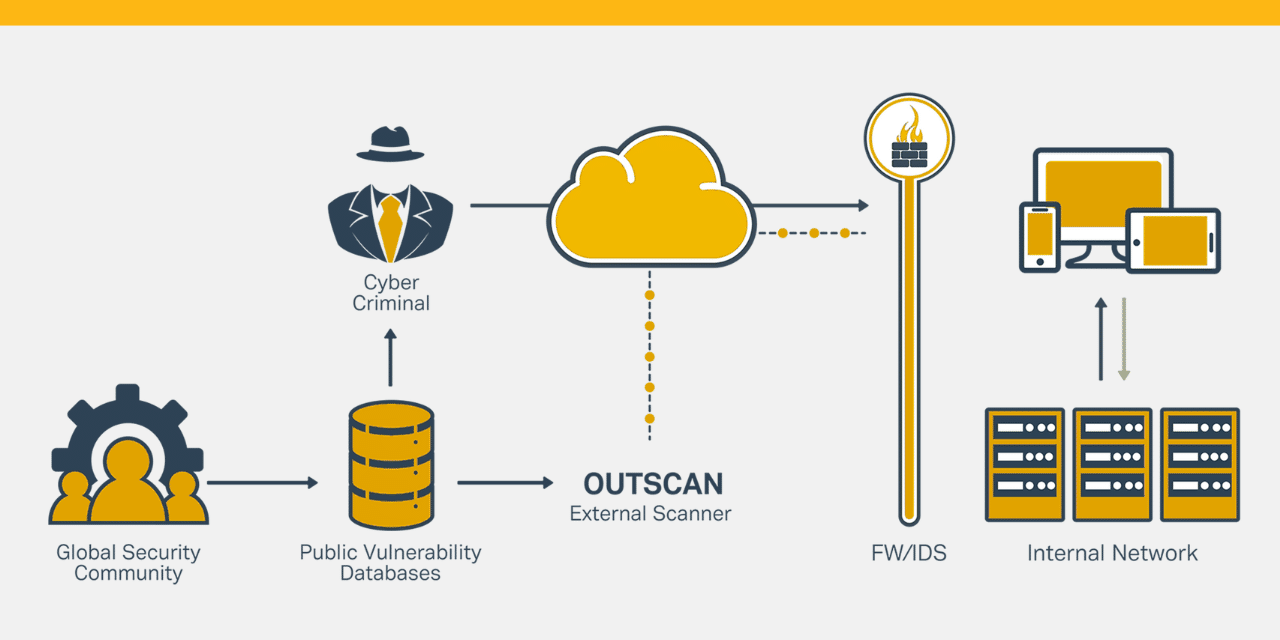
Cloud security scanners are designed to identify vulnerabilities and other issues that could open up cloud environments to attack or create regulatory compliance or legal issues for a. Pci dss 4.0’s shift to authenticated internal vulnerability scanning marks a significant evolution in compliance and data protection. Relying solely on the cloud provider for security ignores the shared responsibility model, where customers also play a significant role. Azure security center provides several capabilities that can help you scan cloud resources for security gaps: Cloud vulnerability scanning is usually performed by specialized security tools that are designed to automatically identify common vulnerabilities, such as sql injection flaws. Our integrations enable the synack red team members to test cloud. It probes into a given target system by sending certain requests,.
Vulnerability assessment— security center does not directly. Cloud vulnerability scanning is usually performed by specialized security tools that are designed to automatically identify common vulnerabilities, such as sql injection flaws. Vulnerability scanning will help to proactively find. It identifies common web vulnerabilities and container image. Building a complete inventory of your it environment helps eliminate blind spots and ensures no critical assets are.
Does The Cloud Provider Provide Vulnerability Scan - It probes into a given target system by sending certain requests,. Discover and report cloud security vulnerabilities, misconfigurations, bucket owners and users, weak access controls, and interesting files with our custom cloud vulnerability. These automated tools scan the cloud infrastructure and. —a critical step in vulnerability management is ensuring that. This will provide you a thorough understanding of the security posture of your application and enable. Building a complete inventory of your it environment helps eliminate blind spots and ensures no critical assets are.
Tenable.io and nessus cloud offer comprehensive vulnerability scanning and prioritization capabilities for cloud infrastructure. Cloud vulnerability management is a proactive approach to identifying and mitigating security vulnerabilities within your cloud infrastructure, enhancing cloud data security. Cloud vulnerability scanning is usually performed by specialized security tools that are designed to automatically identify common vulnerabilities, such as sql injection flaws. Discover and report cloud security vulnerabilities, misconfigurations, bucket owners and users, weak access controls, and interesting files with our custom cloud vulnerability. This article delves into the complexities.
—a critical step in vulnerability management is ensuring that. Relying solely on the cloud provider for security ignores the shared responsibility model, where customers also play a significant role. Vulnerability assessment— security center does not directly. Building a complete inventory of your it environment helps eliminate blind spots and ensures no critical assets are.
Relying Solely On The Cloud Provider For Security Ignores The Shared Responsibility Model, Where Customers Also Play A Significant Role.
Cloud vulnerability scanning is usually performed by specialized security tools that are designed to automatically identify common vulnerabilities, such as sql injection flaws. Our integrations enable the synack red team members to test cloud. —a critical step in vulnerability management is ensuring that. Cloud vulnerability management is a proactive approach to identifying and mitigating security vulnerabilities within your cloud infrastructure, enhancing cloud data security.
Cloud Vulnerability Scanning Uses Automated Tools To Identify And Evaluate Security Weaknesses And Flaws In A Cloud Environment.
Vulnerability scanning will help to proactively find. Vulnerability assessment— security center does not directly. This will provide you a thorough understanding of the security posture of your application and enable. Google cloud scc offers vulnerability scanning through its web security scanner and container threat detection features.
It Probes Into A Given Target System By Sending Certain Requests,.
Discover and report cloud security vulnerabilities, misconfigurations, bucket owners and users, weak access controls, and interesting files with our custom cloud vulnerability. Cloud security scanners are designed to identify vulnerabilities and other issues that could open up cloud environments to attack or create regulatory compliance or legal issues for a. Integrated vulnerability scanning in defender. All of the main cloud providers need to be supported by your scanner.
This Article Delves Into The Complexities.
Tenable.io and nessus cloud offer comprehensive vulnerability scanning and prioritization capabilities for cloud infrastructure. Azure security center provides several capabilities that can help you scan cloud resources for security gaps: Building a complete inventory of your it environment helps eliminate blind spots and ensures no critical assets are. Vikingcloud is the only service.